What to Do After a Data Breach: Essential Recovery Steps

TL;DR
- If your data is exposed in a breach, act quickly to secure passwords and financial accounts.
- Enable multi-factor authentication and monitor accounts for suspicious activity.
- Check breach databases and update passwords to reduce the risk of account takeover.
Introduction
What to do after a data breach is one of the most important things to understand if your email, password, or personal information has been exposed online. A fast response can help you secure your accounts, prevent identity theft, and stop a bad situation from getting worse.
Unfortunately, data breaches are now a normal part of digital life. Companies get hacked, customer records get leaked, and stolen credentials often spread quickly across cybercriminal networks.
The good news is that you do not need to panic. You just need a clear plan. Once you know what to do after a data breach, you can take practical steps to protect your accounts, your money, and your digital identity.

What to do after a data breach means securing affected accounts, changing exposed passwords, enabling multi-factor authentication, and monitoring financial or personal activity for signs of fraud or identity theft.
Understanding What Happens After a Data Breach
A data breach happens when hackers or unauthorized parties gain access to sensitive information stored by a company, app, or online service.
The exposed data may include email addresses, passwords, phone numbers, home addresses, payment card details, or other personal information.
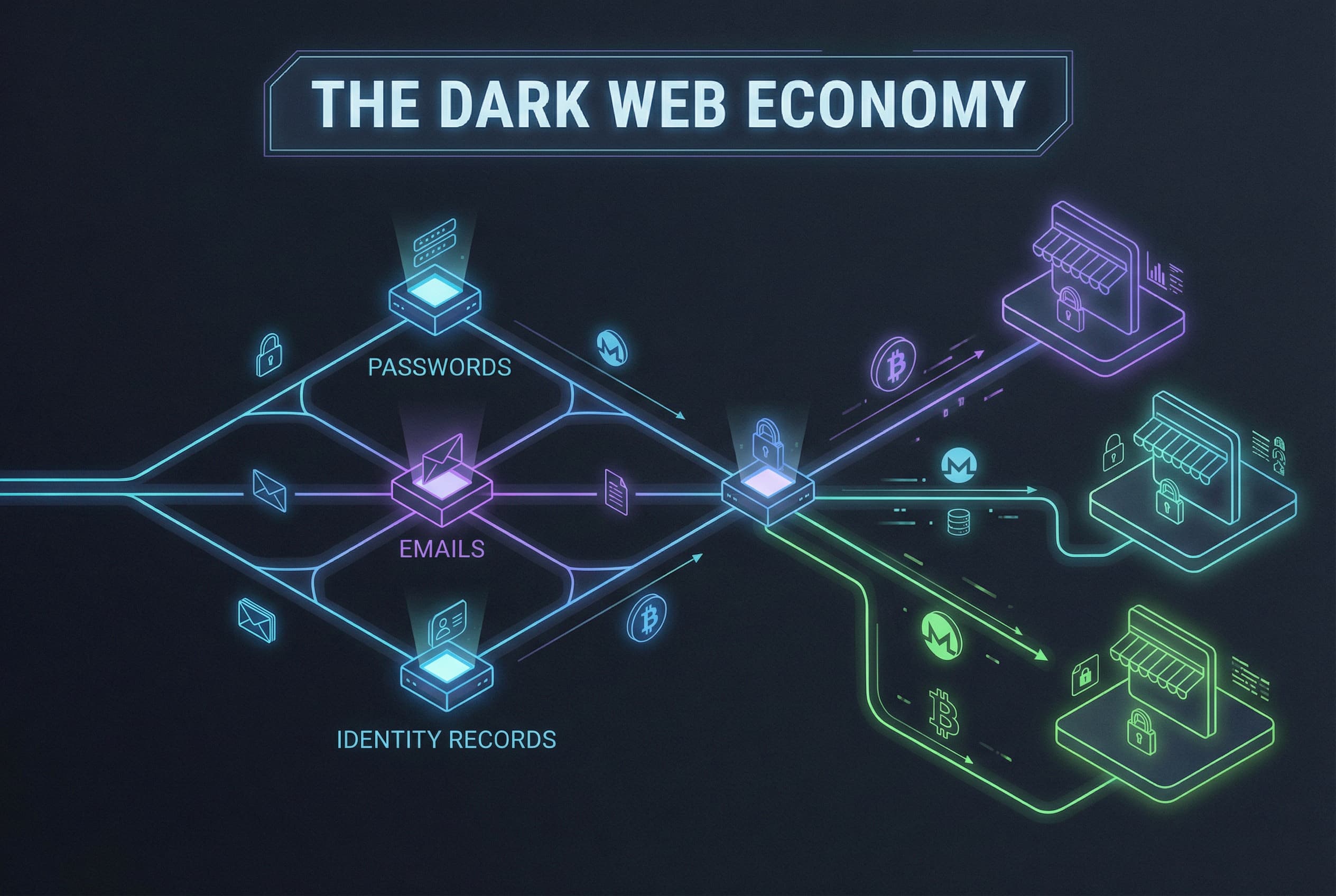
Once that information is stolen, it can be sold, shared, or used in other attacks. In many cases, leaked credentials end up in breach databases or underground marketplaces where criminals look for easy ways to break into additional accounts.
This is where password reuse becomes especially dangerous. If the same password is used across multiple platforms, one breach can lead to account takeover on several services at once.
Why This Happens
Some breaches happen because a company has weak security, outdated software, or poor internal protections. Other times, attackers gain access through phishing, malware, or stolen employee credentials.
But personal habits matter too. Reusing passwords, ignoring breach alerts, and clicking suspicious links all make it easier for attackers to turn one security incident into a much larger problem.
According to Experian’s breach recovery guidance, one of the most important first steps is changing passwords quickly and watching accounts for unusual activity.
That advice matters because cybercriminals do not always use stolen data right away. Sometimes they wait, test credentials on other sites, or combine leaked information with phishing scams later.
Risks You Should Know
The most immediate risk after a breach is account takeover. If hackers have your login details, they may try to access your email, bank account, shopping apps, or social media profiles.
Email accounts are especially valuable because they can be used to reset passwords for everything else. Once someone controls your inbox, they can often work their way into other accounts fast.
There is also the risk of identity theft. If enough personal details were exposed, criminals may try to open new accounts, commit fraud, or impersonate you online.
This is part of why it helps to understand how data breaches happen in the first place. The more clearly you understand the risks, the faster you can respond in the right way.

How to Protect Yourself: What to Do After a Data Breach
If you receive a breach alert, or suspect your information may have been exposed, take these steps as soon as possible.
1. Change the Affected Password Immediately
Start with the account named in the breach notice. Replace the password with a new one that is unique and not reused anywhere else.
If you used that same password on other accounts, update those too. This is one of the most important steps after data breach exposure because it prevents credential stuffing attacks from spreading.
2. Turn On Multi-Factor Authentication
Multi-factor authentication adds a second layer of protection beyond your password. Even if someone has your login credentials, they still need the extra verification step to get in.
This is one of the simplest ways to reduce the chance of unauthorized access after a personal data breach recovery process begins.
3. Review Financial Activity Carefully
Check your bank accounts, credit cards, payment apps, and subscription charges for anything unusual.
Consumer Reports recommends monitoring statements closely after a breach because early detection can make fraud easier to stop.
4. Watch for Phishing and Scam Messages
After a breach, attackers often send fake password reset emails, security warnings, or text messages pretending to help. These scams are designed to trick people who are already worried.
Be cautious with links, attachments, and urgent messages. A breach often leads to more phishing attempts, not fewer.
5. Check Where Your Data Has Been Exposed
Look for trusted breach notification tools or services that help identify whether your email or login details appear in known leaks.
This can help you understand which accounts may need attention and where to secure accounts after breach exposure more aggressively.
6. Start Using a Password Manager
Password managers make it much easier to create and store strong, unique passwords for every account.
That way, one leaked credential does not put your entire digital life at risk. This is one of the best long-term ways to protect yourself after a breach.
Why This Matters for Your Online Security
A single breach can trigger a chain reaction. Stolen passwords can lead to account takeovers, phishing attacks, financial fraud, and larger identity theft issues.
That is why learning what to do after a data breach is really about more than one incident. It is about building stronger digital habits that protect you across all the accounts you use every day.
If you want broader context, our guide to modern cyber threats explains how these attacks fit into the larger online security landscape.
You can also read more about how stolen credentials circulate on the dark web, where breach data often gets traded and reused.
TREASURELY Perspective
Most people are not bad at security. They are just overloaded. Between work apps, shopping accounts, banking tools, and social platforms, it is easy for digital safety to feel like one more exhausting task.
TREASURELY believes better online protection starts with making safer habits easier to maintain. Password security, breach awareness, and identity protection should feel clear, practical, and built for real life.
Digital safety works best when it is something people can actually stick with.
Related Guides
If you want to go deeper, explore our guides on how data breaches work, where stolen information ends up, and how broader cyber threats affect your online life.
Stay Ahead of Digital Threats
Want more practical guidance on what to do after a data breach and how to strengthen your online security overall?
Subscribe to the TREASURELY newsletter for breach alerts, digital safety insights, and smarter password protection tips that help you stay protected online.
Related Posts
Stay Ahead of Cyber Threats
Get weekly security tips, scam alerts, and digital privacy advice from TREASURELY.