Why Is Password Theft More Valuable to Hackers Than Money?

TL;DR
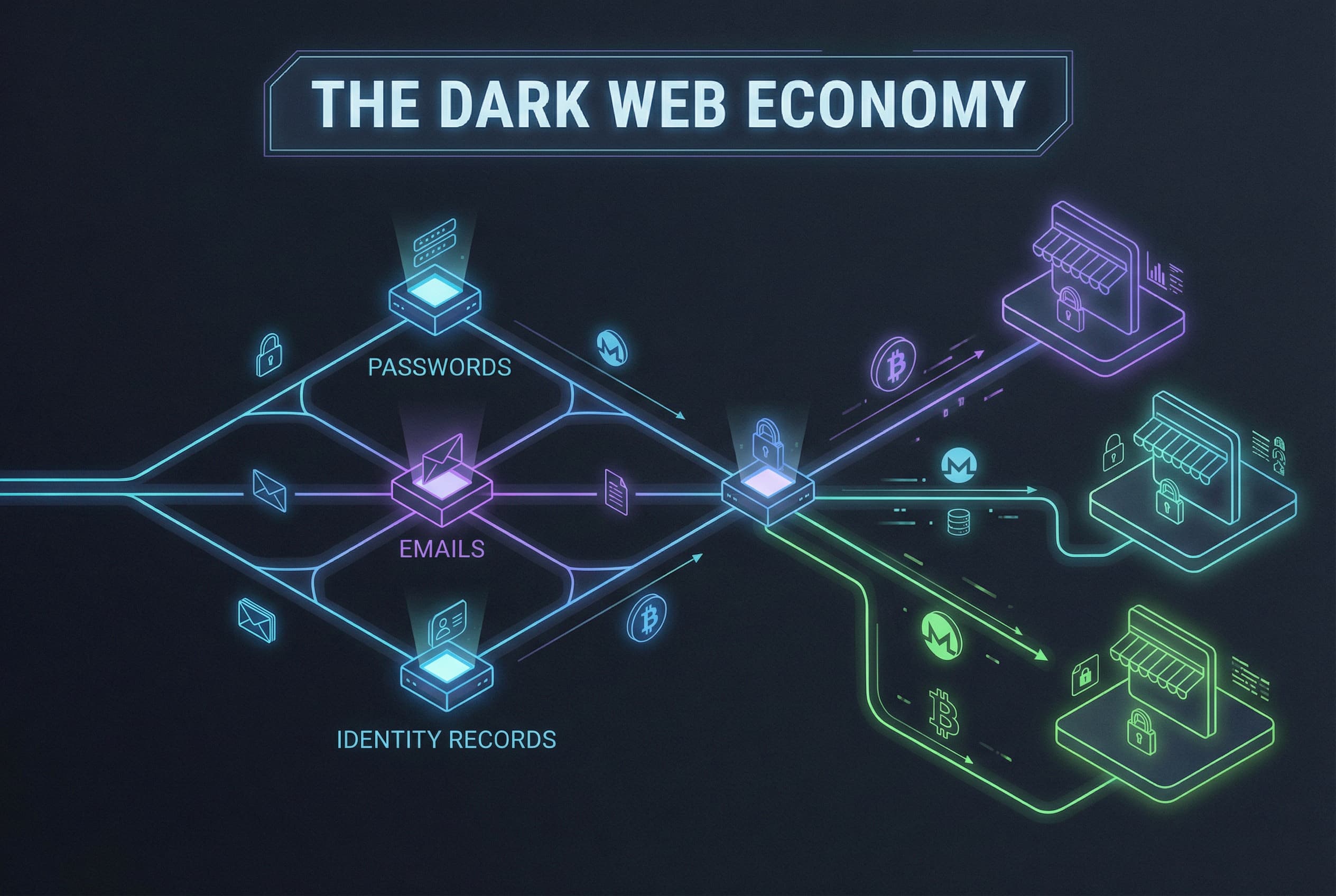
- Password theft is one of the most common ways hackers gain access to accounts, identities, and personal data.
- Stolen credentials are often more valuable than direct financial theft because they unlock entire digital ecosystems.
- Small security habits like stronger password management and multi-factor authentication dramatically reduce risk.
Why Is Password Theft More Valuable to Hackers Than Money?
Most people assume cybercriminals are trying to steal money.
However, modern cybercrime often revolves around something far more powerful: password theft.
Password theft gives hackers the keys to entire digital identities. Email accounts, cloud storage, social media, streaming platforms, and financial services often connect through the same set of credentials.
Once attackers gain access to those credentials, the damage can expand quickly.
This is why credential theft has become one of the most common entry points for cybercrime. Research highlighted by CrowdStrike shows that stolen credentials are frequently used in major cyberattacks because attackers can log in quietly rather than break into systems.

In other words, password theft lets attackers skip the complicated hacking.
They simply sign in as you.
What Is Password Theft?
Password theft occurs when attackers obtain login credentials without permission.
This can happen through phishing messages, malware, fake websites, data breaches, or social engineering.
Once credentials are captured, they often become part of larger credential theft campaigns.
According to Palo Alto Networks, credential-based attacks rely heavily on the reality that many users reuse passwords across multiple services.
This means one stolen login can unlock several accounts.
And for cybercriminals, that makes password hacking extremely efficient.
How Do Hackers Actually Steal Passwords?
Phishing Attacks
Phishing is one of the most common password theft methods.
Attackers send emails or messages pretending to be trusted companies. Victims are directed to fake login pages where credentials are captured.
Because these pages often mimic real services perfectly, even experienced users sometimes fall for them.
Data Breaches
When organizations experience breaches, databases containing user credentials may be exposed.
Even encrypted passwords can sometimes be cracked or reused in other attacks.
Cybercrime research from the University of Maryland highlights how stolen credentials from breaches frequently circulate in underground markets.
Credential Stuffing
Once attackers obtain stolen credentials, they test them across dozens or even hundreds of websites automatically.
This strategy works because many users reuse passwords.
A single password theft event can therefore unlock multiple accounts.
Malware and Keyloggers
Malware can secretly record everything typed on a device.
When a victim logs into an account, the password is captured instantly.
These programs often arrive through infected downloads or malicious browser extensions.
Fake Login Websites
Some password hacking campaigns create realistic copies of legitimate websites.
Users believe they are signing into a real platform, but they are actually handing credentials directly to attackers.

Public Wi-Fi Interception
On unsecured public networks, attackers may intercept login traffic.
If encryption protections are weak, credentials can sometimes be captured while being transmitted.
Social Engineering
Not every password theft attack relies on technology.
Some attackers simply manipulate people into revealing credentials through fake support calls or urgent security warnings.
Password Harvesting Malware
Certain malware specifically targets stored credentials in browsers or password files.
According to Dashlane, these tools can extract saved passwords directly from infected devices.
Why Password Theft Is So Valuable to Cybercriminals
Modern digital life revolves around accounts.
Most people now manage dozens of services including banking, shopping, work platforms, and communication tools.
Every account requires credentials.
This means stolen credentials can unlock a huge portion of someone’s online life.
Cybercriminals recognize this.
Instead of attacking complex systems directly, they focus on obtaining passwords.
Once inside an account, attackers may gather personal data, reset other passwords, or even launch further scams.
And because the login appears legitimate, many of these attacks remain invisible for weeks.

How to Reduce Your Risk of Password Theft
Use Unique Passwords
Reusing passwords creates chain reactions during credential theft incidents.
If one account is compromised, attackers can access others quickly.
Enable Multi-Factor Authentication
Two-factor authentication adds an additional verification step beyond passwords.
This dramatically reduces the success rate of password hacking attempts.
Be Cautious With Login Links
If an email or message asks you to log in urgently, verify the website address before entering credentials.
Many phishing pages rely on urgency to bypass caution.
Monitor Breach Notifications
Breach alerts help identify when credentials may have been exposed.
Changing passwords quickly can stop attackers from using stolen credentials.
Use Smarter Password Management
Managing dozens of strong passwords manually is difficult.
Modern password tools simplify this process while improving security.
The Future of Digital Security Should Be Easier
Cybersecurity tools historically emphasized complexity.
However, the reality is that people need security systems that fit naturally into everyday life.
When protecting passwords becomes simple and intuitive, adoption increases dramatically.
This shift toward human-centered cybersecurity is shaping the next generation of digital safety tools.
The goal is not just stronger protection.
It is security that people actually want to use.
Stay Ahead of Password Theft
Password theft remains one of the most common ways cybercriminals access digital accounts.
The good news is that awareness and a few strong habits dramatically reduce the risk.
If you want more insights into modern digital safety, emerging breach trends, and smarter ways to protect your online life, subscribe to the TREASURELY newsletter.
We break down cybersecurity in ways that actually make sense.
Related Posts
Stay Ahead of Cyber Threats
Get weekly security tips, scam alerts, and digital privacy advice from TREASURELY.